Introduction
In an era where personal data is constantly under threat, effective access control is essential to ensure the privacy and security of our digital lives. One of the most promising solutions to this challenge is Near Field Communication (NFC) authentication on Android devices. This technology offers a convenient and secure way to unlock your Android device and protect your data from unauthorized access. In this blog post, we will explore the benefits and implementation of NFC authentication for enhanced Android access control.
Passwords - the bain of users and help desks everywhere
If you’ve ever spent time working as a help desk support engineer, you know that one of the most frustrating calls you can get is from a user who has forgotten their password. Users simply want to get into their system and access their applications so that they can get their job done. Check out our SSO guide here!
These problems can be even worse if they have to work from a shared mobile device. The small screen size, in addition to most enterprises’ complex security requirements, makes it practically inevitable that users will get locked out of their account at some point or another. Not only is this frustrating for employees, but it puts a significant strain on productivity and support costs.
Some analysts estimate that up to 50% of help desk calls are related to password resets for enterprises. With the cost of a password reset ranging between a few dollars and hundreds of dollars, it’s no wonder that these expenses can quickly add up and cause a big hit on the bottom line.
Unfortunately, there is no silver bullet that allows companies to eliminate all passwords, but there are steps that can reduce password issues. Some examples we’ve talked about in the past include implementing SSO to prevent having users login multiple times or leveraging AI/ML to recognize authentication threats and improve security. One of the newer trends companies are adopting is leveraging physical tokens with mobile devices to support password-less authentication. The most common mechanism uses near-field communication (NFC). Solve enterprise Android password challenges – Contact Bluefletch for solutions!
What is NFC?
Near Field Communication (NFC) is a short-range wireless communication technology that enables simple and secure interaction between devices. It allows devices to communicate by bringing them close together, typically within a few centimeters. NFC is commonly used for contactless payments, identification, and data transfer.
Enhanced Access Control with NFC Authentication:
NFC authentication enhances access control on Android devices by leveraging the built-in NFC capabilities. With NFC authentication, users can unlock their devices by simply tapping a NFC-enabled token or card. This eliminates the need for traditional passcodes or patterns, providing a more convenient and secure method for authentication.
Benefits of NFC Authentication:
- Ease of Use: NFC authentication simplifies the unlocking process. Users only need to tap their NFC-enabled token against the device, eliminating the need to remember complex passcodes or patterns.
- Enhanced Security: NFC authentication provides an extra layer of security compared to traditional authentication methods. It is less susceptible to common threats like password guessing or shoulder surfing. Additionally, NFC authentication requires physical proximity, making it harder for an unauthorized user to gain access to the device.
- Two-Factor Authentication (2FA): NFC authentication can be combined with other authentication methods, such as a PIN or biometric authentication, to create a robust two-factor authentication system. This adds an additional level of security that further protects sensitive data.
Implementing NFC authentication on Android devices involves a few simple steps:
- Enable NFC: Ensure that NFC is enabled on the Android device by going to the device’s settings menu.
- Set up NFC Token: Associate an NFC-enabled token, card, or key with the Android device. This can be done by following the instructions provided with the NFC token or card. It usually involves tapping the token against the device to establish a connection.
- Configure Android Security Settings: In the Android device’s security settings, enable NFC as an authentication method. This allows the device to recognize the NFC token and use it for unlocking.
- Test and Use: Once the NFC token is set up and configured, test it by tapping it against the device. If successful, the device should unlock, providing access to the user’s data and applications.

The basic premise of an NFC tag is that you have to be within a few centimeters (up to 4 inches) to read a tag. This proximity makes them a decent option as an authentication token since they can only be read from close by. Additionally, most modern mobile devices have started to include a built-in NFC antenna for reading and writing NFC tags.
Authentication for users is typically preferred with one or more of the following:
- Something you know (a password, PIN, or phrase)
- Something you are (face recognition, voice print, or fingerprint)
- Something you have (a token, key, or badge)
Leveraging NFC for authentication (or for 2-factor auth) falls into the last category. Recently, a standard called FIDO2 has been evolving, which allows for NFC keys or USB keys to be used as a secure authentication source.
The most significant advantage of using a token for authentication is that the user doesn’t have to type in their password every time, which not only reduces the time it takes to log in, but it also reduces the number of help desk tickets pertaining to locked accounts or password resets.
BlueFletch supports leveraging NFC tags for authentication in our Android Enterprise Launcher. NFC can be used for re-authentication or as a secondary authentication mechanism. We have found this most practical in shared device scenarios where users might use a device for short bursts throughout their shift. With this solution, users can pick up a device and quickly re-authenticate (even if the device has become locked). Streamline authentication on Android devices – Schedule a strategy session now!
Overview of BlueFletch Launcher NFC Authentication
The BlueFletch Enterprise Launcher is a secure replacement for the Android home screen. It helps companies lockdown settings and secure apps on shared devices. Take a look at this overview if you are interested in learning more.
Since this article is about NFC authentication, we are going to skip over details about SSO and Identity Provider integration and just focus on how we’ve approached leveraging NFC for user authentication.
How the solution works
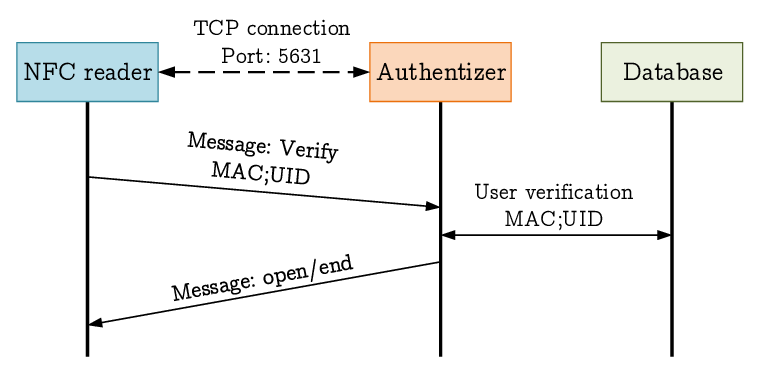
The BlueFletch NFC Authentication process is designed not to require anything other than a mobile device and a MiFare NFC tag/badge. If a user wants to associate a new NFC tag for authentication, they will tap their NFC badge on the device when it is on the login screen, and the device will prompt them to enter their credentials manually. This initial step creates a secure encrypted association of the NFC tag with the User ID.
After the system validates the user has logged in at least once using NFC, the user will be able to leverage their NFC badge to log into any other devices within the organization. The user will be able to leverage NFC login until a predetermined amount of time set by your security admins for your IDP.
The NFC authentication solution also supports rapidly switching users on shared devices. For instance, if “BobSmith” is currently logged into a device and “JohnDoe” taps his badge on the device, it will logout BobSmith and instantly log “JohnDoe” onto the device.
Built with end-to-end security
The focus of a token authentication process should be to make authentication as secure as possible. The BlueFletch Enterprise Launcher encrypts the data by using a combination of a Private Key deployed to the device, along with the actual NFC data. The encrypted hash is unique per customer and user.

The session information is encrypted before it leaves a device and is sent to the authentication store, making it impossible to access the encrypted data without the users’ NFC badge. If the user happens to lose their badge, they will need to log in with the full password and associate a new badge with the authentication session. If a badge is lost or stolen, it will be revoked when the user associates a new badge. Likewise, if a user is removed from the Identity Provider they will no longer be able to login with the NFC badge.
Supported Identity Providers
Supported Hardware
To be able to leverage NFC authentication, you need to have a device with an NFC antenna that supports reading and writing. Most of the devices we have tested from Zebra Technologies, and Honeywell performed well for leveraging NFC tap to log in. If you have specific questions about hardware support, reach out to our support team at info@bluefletch.com
In Conclusion: Balance Security and User Experience
In a world where data breaches and unauthorized access are constant threats, it is crucial to implement robust access control measures on our Android devices. NFC authentication offers a convenient and secure solution by leveraging the built-in NFC capabilities. Its ease of use, enhanced security, and compatibility with two-factor authentication make it an appealing choice for Android users looking to maximize their device’s security. By following a few simple steps, users can enable NFC authentication and unlock their devices with a simple tap, ensuring the privacy and security of their personal data.
The security of enterprise mobile devices can no longer be an afterthought. These devices have become powerful tools with access to critical resources within companies’ infrastructure. At the same time, security should not be allowed to hinder an employee’s ability to perform their work with the best experience possible. Enhance security and user experience on enterprise Android – Let our experts help!
IT organizations must continue to refine their approach to supporting advanced security mechanisms like NFC authentication or FaceRec Authentication to ensure their employees can take advantage of mobile technology with as little friction as possible.
If you would like to learn more about our NFC single sign-on solution, feel free to email our team at info@bluefletch.com








