Over that last nine years, Android has gone from being perceived as a “cheap half-baked mobile platform” to being the mobile platform of choice for companies looking to deploy dedicated devices to their end-users. Apple iOS devices are viewed as premium devices and have a specific set of niches where they outperform Android (such as the tablet space). Still, Android has taken a dominant hold in the company-owned dedicated device space.

The reasons for companies going with Android include:
- Control of Device – With Android, you have much more control over the behavior and experience of the device than you do with iOS.
- Development Ecosystem – The development tools for Android are free and can run on any operating system (Windows, Mac, Linux).
- Hardware Variety – The form factors for android devices range from watches and small chip-level boards up to full-sized kiosk screens.
- Faster Time to New Accessories – Due to the variety of vendors in the Android ecosystem, new technology features are typically available on Android hardware before they become available on iOS (examples include NFC, 5G, new Wifi standards)
- Rugged Device Options – There are some great rugged android device options available the have great drop specs and waterproofing. There are even some devices that are specifically designed for oil and gas environments.
- Price Point – There is a wide range of device price points available. Some reputable android devices can cost less than 200 dollars per unit.
- Platform Flexibility – You have a lot of options for configuring the software, settings, and experience on android devices. From the look and feel to how the device
The downside of the last item (flexibility of the platform) is that it can create potential vulnerabilities that can increase your exposure to a breach. As enterprises begin to add more Android devices to their technology landscape, the security of these devices needs assessment.
The following are three core areas that we recommend you address for your dedicated device security posture:
1. Replace the Android Launcher on Your Devices
On Android devices such as the “launcher” is the home screen that controls access to all the applications on the device. You may have noticed that most consumer Android devices have differences in their home screen UI experience; this is because different vendors (Samsung, Motorola, HTC) all have created variants of launchers that they put on devices. You can replace the launcher on Android devices with an aftermarket or specialized launcher. Popular aftermarket launchers you will find in the consumer space include Nova Launcher, Blackberry launcher, Smart Launcher, Action launcher. These launchers have different features and customizations that give users the flexibility to optimize their android devices for how they would like to use them.
Why you should replace your devices' launcher:
For enterprise devices, most rugged devices come with a reasonably standard launcher that looks close to what you would find with the Stock Google launcher. We recommend replacing this launcher with a more secure version that hardens and locks down your devices. Features that you will find in a secure launcher can include: controlling setting access, controlling notifications access, requiring PIN/password for device access, and controlling what applications users can access.
How to replace launcher:
Most manufacturers include a launcher that you can leverage for their devices such as the Zebra Enterprise Home Screen, The Honeywell Launcher, or the Datalogic Lockdown launcher. Manufactures’ launchers do a good job of setting devices in a single configuration kiosk mode.
If you are looking for more advanced launcher features, you can look to see if your MDM includes a launcher. VMware WorkspaceOne includes the AirWatch Launcher, which has some single sign-on capabilities and customization based on the device’s MDM profile. SOTI MobiControl also offers a launcher that can provide users with some sign-on capabilities. You can also look to a 3rd party launcher like BlueFletch’s Enterprise Launcher if you are looking for more advanced configuration and 3rd party Identify Provider integration. Lastly, if you cannot find a viable option, you can build a custom launcher customized to your business’s particular use case.
2. Implement SSO Login For your Devices
Single Sign-On (SSO) is a terminology used to describe the technology where all of your applications share the same login credentials for a user. Additionally, once a user logs in to one application, they can access other apps in the same session without having to re-enter their password every time. SSO means that every user has only one password to remember. The key SSO vendors that we have been running across in the enterprise space include Okta, PingIdentity, Microsoft ADFS / Azure AD, OneLogin, and Google Auth.
Why should you implement SSO for your mobile devices? There are several reasons, but the primary ones include:
- Shared passwords create holes – According to a 2018 study by Verizon, 80% of company breaches are the result of bad passwords or poor password management. If users have shared passwords to access devices, it is likely that the password is already on the internet. A shared password is almost worse than no password because it creates a false sense of security.
- One user per login creates accountability – When one of our clients rolled out individual logins, we saw the traceability of devices back to users creates a drop in “Lost” devices of over 7%.
- Users will write down passwords – If users have to log into multiple apps with different credentials, the likelihood of them writing down their password goes up substantially.
- Password management is expensive – if users have to remember more passwords, the likelihood of them forgetting password and requiring a password reset goes up. According to recent research from Okta, the total cost for productivity and support resource for a password reset averages around $70 per incident.
To implement SSO, you will need three things:
- Choose your identity and SSO Provider – most large organizations already have a system that allows them to create login ids for employees; Active Directory (AD) is the most common one we run across. On top of that, you can bolt on an identity solution such as Okta or Ping that will handle authentication validation and creation of tokens.
- Applications to Support SSO – applications need to be able to accept SSO tokens or be able to handle the login process. You can use a custom SDK from your identity solution provider, or you can leverage custom chrome tabs. For some legacy providers, we have had to create a proxy authentication service that runs locally on a device to handle SSO.
- A login process to handle authentication – the two approaches we have seen for login processes are to force a login event for the first app the user opens or to leverage an Android Launcher to perform the initial sign-on.
Once you implement your SSO solution, you can do further analysis and tweaking to optimize the authentication of your users. You can even test leveraging AI to model employee behavior and identify when you need to prompt for different levels of authentication.
3. Control the Settings on Devices.
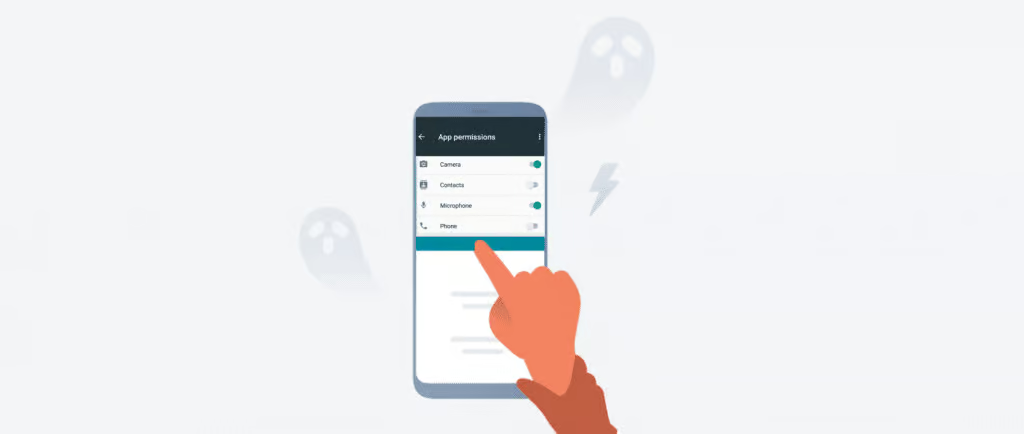
One of the significant advantages of Android that I mentioned above was the variety of options available on the platform. The number of configuration options when it comes to settings can also be a downside when it comes to security. When left uncontrolled, I have observed all sorts of changes in settings on mobile devices. Employees may change settings to try to make their experience better or, in some cases, may change settings just to make a device unusable. The more dangerous changes we have seen users make include:
- Network changes – We have seen users put devices on shared public wifi, or we have seen users put devices on non-secured networks. Both of these easily open up your devices as a point of breach.
- Developers Options – By default, your corporate devices should have USB debugging disabled. If this setting is enabled, hackers can easily plug into a mobile device and pull data from it.
- App Installation – For corporate-owned devices, users should not be able to install applications. If given access to settings, a user could change the setting for installing unknown apps, which would allow malware to slip onto your devices.
- App Uninstallation – If a user has access to get to settings, they may have the ability to remove or disable your device management solution (EMM/MDM).
We recommend the following policies for corporate-owned dedicated devices:
- Restrict access to settings – Users should not be able to get to the settings app in Android. You should restrict access to this app through both the standard icon and the pull-down notifications menu.
- Restore Defaults – For settings that you allow users to change (e.g., Volume, Brightness, BlueTooth), build a process to reset those settings back to a standard level when the user’s shift completes.
- Monitor Changes – Build a process for reporting and reviewing settings across your fleet.

